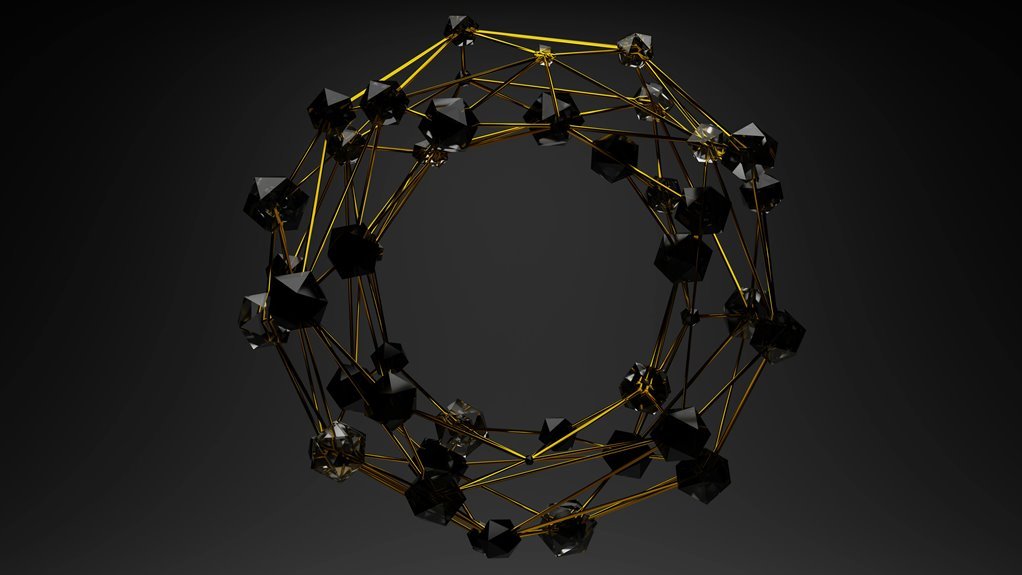
Cyber Node 2145508028 Quantum Prism
Cyber Node 2145508028 Quantum Prism blends quantum-enhanced processing with classical routing. It claims faster key exchange and streamlined authentication through quantum-classical coordination. Skeptics question interoperability, verification, and governance. Interfaces rely on QKD, entanglement correlations, and error correction, yet depend on trusted nodes and transparent metrics. Deployment faces regulatory, supply-chain, and ROI concerns. The practical value remains uncertain, and the approach invites scrutiny before wide adoption can be considered.
What Cyber Node 2145508028 Quantum Prism Is
A Cyber Node 2145508028 Quantum Prism is a discrete, networked component that integrates quantum-enhanced processing with traditional cyberspace routing and data handling.
The description remains cautious: a cyber node that promises efficiency yet requires scrutiny.
Its implications generate discussion ideas about security, governance, and autonomy, while skeptical observers demand verifiable performance and transparent interfaces for robust, freedom-respecting deployment.
quantum prism.
How Quantum Prism Combines QKD, Entanglement, and Classical Networks
Quantum Prism integrates quantum key distribution, entanglement-based correlations, and conventional networking to enable secure key exchange, correlated state management, and standard data routing over existing infrastructure. The system claims seamless quantum-classical interfacing, yet practical deployment faces interoperability challenges.
Quantum prism integration hinges on robust error correction and trusted node assumptions, while entanglement networking remains contingent on scalable, satellite, or fiber-based links. Skepticism persists.
Benefits: Ultra-Low Latency, Strong Data Integrity, and New Security Models
Ultra-low latency, reinforced by near-real-time quantum-classical coordination, promises faster key establishment and session rekeying compared to conventional PKI flows.
The approach emphasizes data integrity and streamlined authentication, yet skepticism remains about scaling, interoperability, and governance.
Quantum prism offers new security models, potentially reducing exposure to classical attacks while introducing complexity and trust assumptions that may complicate independent verification and freedom-oriented architectures.
Real-World Implications: Industries, Policy, and Adoption Challenges
Real-world deployment of Quantum Prism technologies raises questions about industry applicability, regulatory alignment, and adoption velocity. Institutions assess cyber policy impacts, interoperability risks, and supply-chain transparency, while skeptics cite uncertain ROI and governance ambiguities. Adoption barriers persist despite claimed throughput gains, as standards lag and private-sector incentives clash with public oversight. Freedom-minded observers demand empirical pilots, verifiable metrics, and proportional, rights-respecting deployment.
Conclusion
Conclusion:
Cyber Node 2145508028 Quantum Prism represents a technical stride, yet its promise must be weighed against verifiable interoperability and governance gaps. The architecture’s fusion of QKD, entanglement, and classical routing promises low latency and data integrity, but relies on trusted intermediaries and opaque metrics. Skeptics will demand proportional deployment and robust oversight. Until independent validation and transparent performance benchmarks mature, adoption should be cautious, pragmatic, and constrained to clearly justified use cases.