Secure Tech Contact 0120 407 072 Verified Business Service

Secure Tech Contact 0120 407 072 is presented as a verified, privacy-conscious channel for organizational communication. The system emphasizes identity checks, auditable workflows, and limited data exposure to reduce impersonation and fraud. Support efficiency claims hinge on evidence-based processes and continuous governance. Yet the balance between accessibility and control remains uncertain, and external audits are touted but not fully disclosed. Stakeholders might find the next details pivotal for assessing real risk and practical viability.
What Is Secure Tech Contact and Why It Matters
Secure Tech Contact is presented as a business service, but its precise nature hinges on the context in which the term appears. The concept centers on facilitating communications between entities, yet definitions vary. Skeptical assessment demands evidence of practicality, reliability, and governance. Secure tech and Verified service claims require verifiable benchmarks, transparent criteria, and independent validation to support freedom from misleading representations.
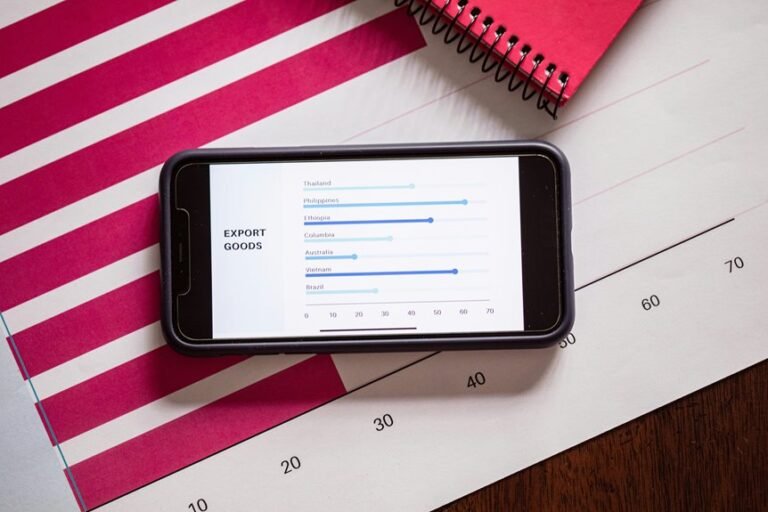
How the Verified Service Prevents Impersonation and Fraud
The verified service aims to reduce impersonation and fraud by imposing verifiable identity checks, auditable processes, and independent validation criteria on communications labeled as Secure Tech Contact.
Skeptical assessment notes that Secure verification procedures constrain ambiguity, publish criteria, and require external corroboration. The result is limited exposure to deception, with measurable fraud prevention outcomes and transparent accountability for participants in the system.
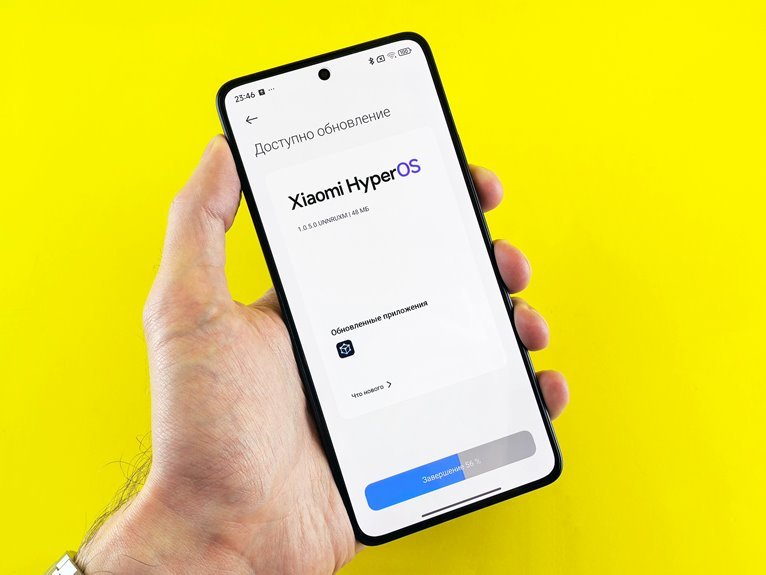
How to Use the Service for Swift Tech Support
Swift tech support workflows leveraging the Secure Tech Contact service proceed only after a verified identity has been established, ensuring that requests originate from legitimate sources.
The process emphasizes secure communication and rigorous user authentication, reducing ambiguity about who requests aid.
While efficiency is valued, procedures remain precise, skeptical of shortcuts, and evidence-based, prioritizing freedom to operate without compromising verifiable accountability.
Best Practices for Maintaining Compliance and Data Safety
How can organizations reliably maintain compliance and data safety in the face of evolving threats and regulations? Rigorous governance frameworks, validated controls, and continuous monitoring form the backbone. The approach favors transparent audits, limited data exposure, and reproducible evidence of security decisions.
Secure privacy requires disciplined data controls, least-privilege access, and verifiable risk assessments under evolving standards. Skeptical, evidence-based, freedom-minded readers demand measurable, repeatable safeguards.
Conclusion
In this tale, a lighthouse keeper wires a door with careful seals and a trusted beacon. The harbor’s fog parts not by bravado but by verifiable signals and audits. Skeptics note every beacon pulse, every access grant, every anomaly logged. When shadows approach, the consistent credentials and reproducible checks prove sturdier than rumor. The service, like the lighthouse, offers evidence-based safety—until the sea itself tests the keeper’s discipline.